-
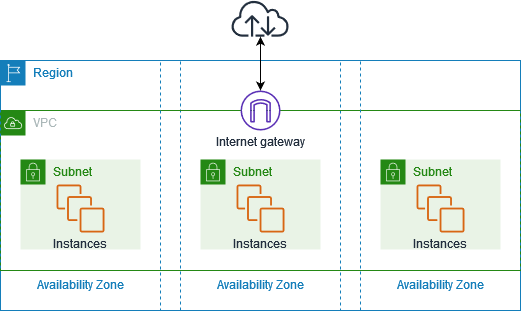
Amazon VPC = logically isolated virtual network in AWS where you control IP ranges, subnets, routing, gateways, and access controls—mirrors a data center network.
-
Key building blocks:
- CIDR blocks (IPv4/IPv6), primary and secondary ranges.
- Subnets (public/private), across Availability Zones.
- Route tables, directing traffic.
- Internet Gateway (IGW), NAT Gateway, Egress-only IGW, Virtual Private Gateway (VGW).
- Endpoints (Interface for PrivateLink and Gateway endpoints).
- Security Groups (instance-level firewall) and Network ACLs (subnet-level stateless rules).
- Compute (EC2, Fargate, Lambda): resources launched inside a VPC, rely on SGs/NACLs for network control.
- Load Balancers (ELB/ALB/NLB) route traffic within VPCs.
- RDS, ElastiCache also deploy inside VPC for network isolation.
- PrivateLink endpoints allow private access to AWS services without internet.
- Transit Gateway for hub-and-spoke connectivity across many VPCs or on-prem networks; VPC Peering for one-to-one links; VPC Lattice (new in 2025) for application-layer connectivity across microservices/multi-account setups with built-in service discovery, auth, load balancing.
- IPAM (IP Address Manager) helps centrally manage IP allocation across accounts/regions.
- Securely isolate workloads (e.g., front-end vs. backend subnets).
- Multi-tier architectures: public-facing services in public subnets, databases in private.
- Hybrid connectivity: VGW for Site-to-Site VPN or Direct Connect.
- Multi-VPC design: use Peering for simple, low-scale; Transit Gateway for complex/hub; VPC Lattice for microservices communication across accounts.
- Access AWS APIs privately using Interface/Gateway endpoints.
- VPC Peering: simple, non-transitive, low-latency point-to-point.
- Transit Gateway: scalable, centralized routing.
- VPC Lattice: modern, layer-7, auth-aware microservices networking.
- IPAM: IP management across fleets.
- PrivateLink (Interface Endpoint) vs. Gateway Endpoint (e.g., for S3, DynamoDB). These alternatives suit different connectivity scales, complexity, or architectural needs.
- VPCs per Region: default 5, adjustable.
- Subnets per VPC: 200 default, adjustable.
- IPv4/IPv6 CIDR blocks per VPC: 5 default, up to 50.
- Elastic IPs per Region: 5; per NAT gateway: 2 (up to 8).
- IGW/Egress-only IGW/NAT Gateway per Region/AZ: defaults vary, adjustable.
- Network ACLs per VPC: 200; rules per ACL: 20.
- Route tables per VPC: 200.
- Routes per route table: previously 50, now 500 by default as of June 2025.
- Security Groups per Region: 2,500. Rules per SG: 60. SGs per ENI: 5 (adjustable up to 16).
- VPC peering connections per VPC: default 50, adjust up to 125.
- Endpoints: Gateway endpoints per Region: 20; Interface/Gateway Load Balancer endpoints per VPC: 50.
- Resource endpoints per VPC: 200.
- Trying to bypass all network-level access controls—VPC doesn’t override IAM or resource-level policies.
- Over-complicating simple systems with multiple VPCs or unnecessary peering/transit gateways.
- Using peering for many-to-many connectivity—better solved by Transit Gateway.
- Using VPC for application-layer service discovery or load balancing—VPC Lattice or ALB is better.
- Deploying systems that don’t require network isolation or need global unisolated networking (e.g., purely serverless public APIs)—simpler architectures may suffice.
- Understand security layers: public vs private subnets, routing via IGW vs NAT, stateless NACLs vs stateful SGs.
- Know connectivity options: Internet Gateway, NAT Gateway, VGW (VPN/Direct Connect), PrivateLink endpoints.
- Distinguish when to choose Peering, Transit Gateway, or VPC Lattice.
- Be able to reason about quotas when designing scale: e.g., route limits (now 500), subnet count, CIDR blocks.
- Expect questions on cost optimization and resilience in network design (e.g., high availability with NAT or IGW across AZs).
- Stay updated: e.g., the default route table capacity change in June 2025—no longer need quota requests for up to 500 routes.
| Aspect | Key Points |
|---|---|
| Definition & Core | Logical isolation, control of IPs, subnets, routes, gateways |
| Integration | EC2, databases, load balancers, endpoints, connectivity services |
| Use Cases | Isolated multi-tier apps, hybrid connectivity, private AWS access, microservices networking |
| Alternatives | Peering, Transit Gateway, VPC Lattice, Endpoints, IPAM |
| Limits | Defaults (VPC:5, subnets:200, route tables:200, routes/table:500, SGs, endpoints...) |
| Misuse | Unnecessary complexity, wrong connectivity choices, ignoring better tools |
| Exam Tip | Master components, connectivity paths, security controls, quotas, and new features (e.g., route limit increase) |