⚙️ Built with ❤️ by BLACK ZERO
🚀 Powered by BANGLADESH CYBER SQUAD
📆 Year: 2025
Next-Generation Parameter Mapping & Discovery Engine
Para-M-Scope (Parameter Mapping Scope) is an asynchronous parameter discovery tool that crawls a target website and extracts parameterized URLs. It is fast, lightweight, and designed for recon and web application mapping in InfoSec workflows.
pkg update -y
pkg install libxml2 -y
pkg install libxslt -y
pkg install python -y
pkg install python3 -y
pkg install git -y
git clone https://github.com/TEAMBCS/Para-M-Scope.git
cd Para-M-Scope
chmod +x *
chmod +w .
chmod 777 *
pip3 install -r para-m-scope.txt
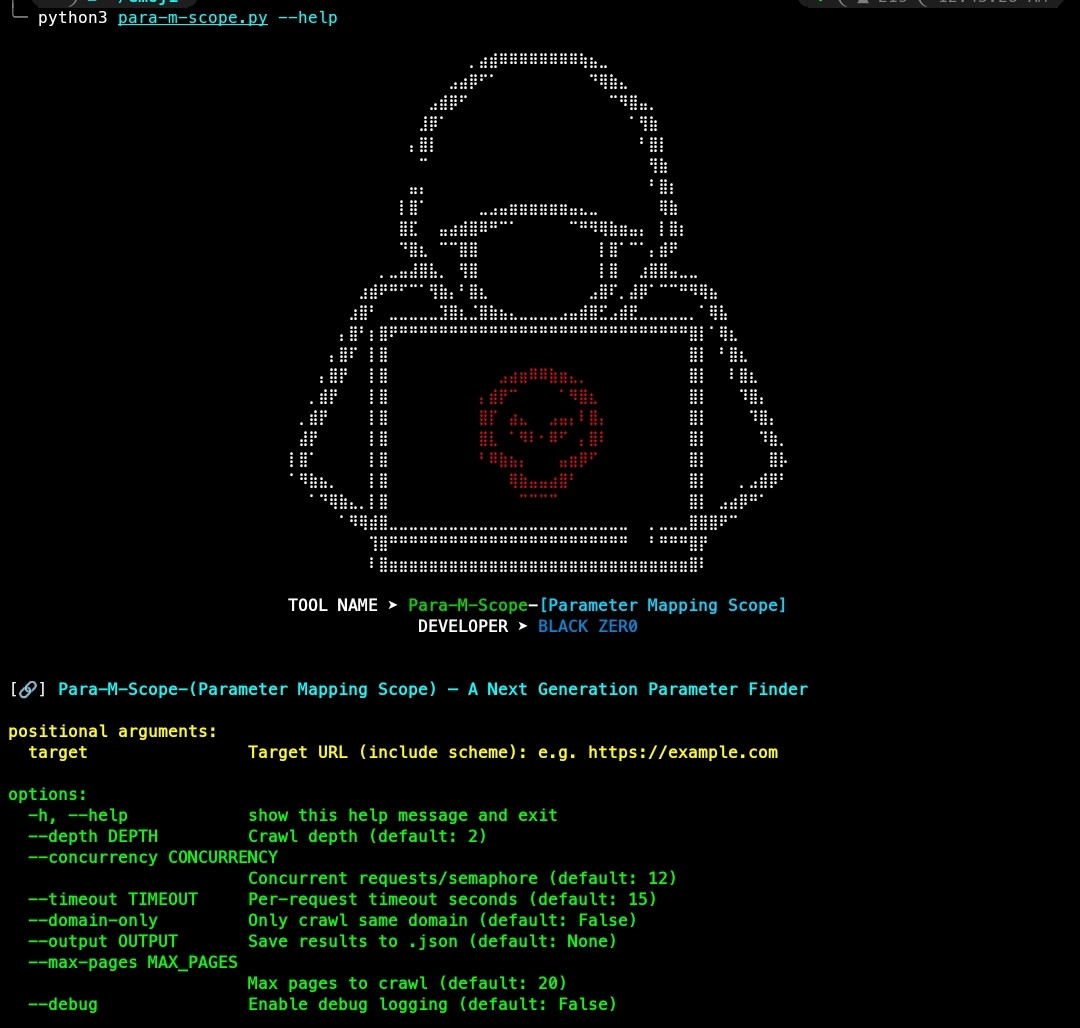
python3 para-m-scope.py --helppip install para-m-scope==1.2.1
para-m-scope -h-
Async crawling using
aiohttpfor high-speed requests. -
Smart link extraction from anchors, forms, scripts, images, link tags and areas.
-
Domain-limited crawling option to stay inside the target domain.
-
Multi-level logging (info, debug, crawl, fetch, params) with a clean datetime format.
-
Suspicious parameter detector for quick XSS / SQL-like pattern hints.
-
New: Parameter analysis features:
- Parameter fuzzing (small payloads) to detect errors / anomalies.
- Reflected parameter detection (potential reflected XSS).
- Common vulnerability keyword detection (SQL/parsing error keywords).
-
Rich table output and optional JSON export.
-
Controls for depth, concurrency, timeout, and max pages.
Para-M-Scope now includes lightweight analysis for each discovered parameterized URL:
-
Parameter fuzzing Appends small payloads (
',",<,>,--) to parameter values and requests the modified URL. Checks for:- Error keywords in the response body (common SQL/parse errors).
- Significant response length changes (heuristic for unexpected output).
- Redirects / changed final URL.
-
Reflected detection Checks whether a parameter value is present in the response body (possible reflected XSS indicator).
-
Common vulnerability keywords check Scans responses for terms like
mysql,syntax error,sqlstate,unexpected token,pdoexception, etc. If found, the tool logs aSUSPECTnote.
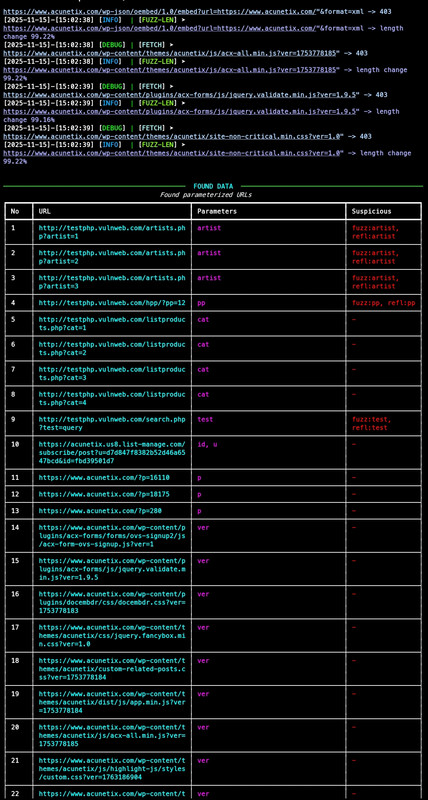
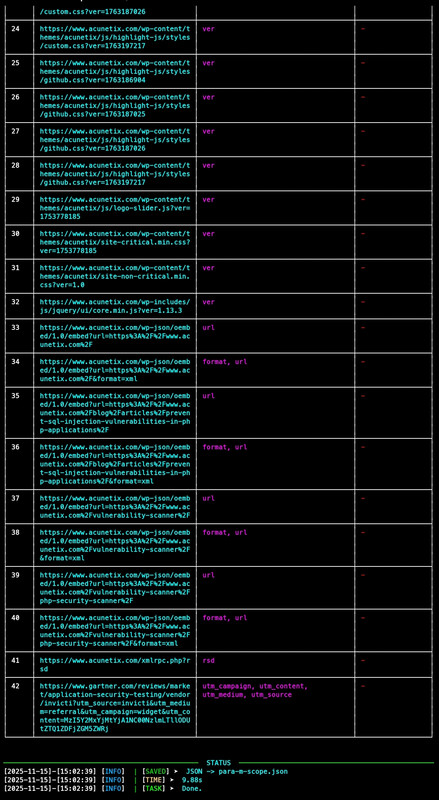
Logs produced include:
PARA-REFLECT— parameter value reflected in response.FUZZ-ERR— fuzzed request produced error-keywords in response.FUZZ-LEN— fuzzed request produced significant length change (>30% by default).SUSPECT— base response already contains error keywords.
Analysis runs asynchronously and non-blocking, so the crawler proceeds while analysis tasks run in background.
Show help:
python3 para-m-scope.py --helpExample:
python3 para-m-scope.py https://example.com --depth 2 --domain-only --concurrency 10 --timeout 20 --max-pages 100 --output results.jsonCommon options
| Flag | Description |
|---|---|
--depth |
Crawl depth (how many link levels to follow) |
--domain-only |
Restrict crawling to the same domain as the target |
--concurrency |
Number of concurrent requests |
--timeout |
Per-request timeout in seconds |
--output |
Save results to the specified JSON file |
--max-pages |
Maximum number of pages to crawl |
--debug |
Enable debug logging |
[2025-01-01]-[19:22:10] [INFO] | [SCOPING] depth=1 -> https://example.com
[2025-01-01]-[19:22:11] [INFO] | [PARA-MS] https://example.com/?id=10 -> ['id']
[2025-01-01]-[19:22:12] [INFO] | [PARA-REFLECT] ➤ [params] https://example.com/?id=10 :: param 'id' appears reflected in response
[2025-01-01]-[19:22:14] [INFO] | [FUZZ-ERR] ➤ [fetch] https://example.com/?id=10' -> keywords ['mysql']
CLI table shows: index, URL, parameter names, and a quick suspicious indicator (reflection/fuzz hints included).
Saved JSON contains generated_at, count, and results. Each result now optionally includes analysis:
{
"generated_at": "2025-01-01T19:25:32",
"count": 1,
"results": [
{
"url": "https://example.com/?id=10",
"params": {"id": ["10"]},
"analysis": {
"reflections": {"id": true},
"fuzz": {
"id": [
{"payload": "'", "final_url": "https://...", "errors": ["mysql"], "len_change_pct": 4.5},
{"payload": "\"", "final_url": "https://...", "errors": [], "len_change_pct": 0.0}
]
},
"error_keywords_in_base": []
}
}
]
}Basic scan:
python3 para-m-scope.py https://target.example --depth 2 --concurrency 8Domain-only scan:
python3 para-m-scope.py https://target.example --depth 3 --domain-only --max-pages 100Save results:
python3 para-m-scope.py https://target.example --output /path/to/results.json-
bs4.FeatureNotFound: lxmlInstall system libs and lxml:pkg install libxml2 libxslt -y pip3 install lxml
-
Session is closedor related aiohttp errors Make sure the script is run normally (asyncio.run(main())) and dependencies are current. Use--debugto get more logs. -
Too many open files(Termux) Increase FD limit and reduce concurrency:python3 para-m-scope.py ... --concurrency 6
-
Slow network / timeouts Increase
--timeout(e.g., 20 or 30).
- Increase file descriptor limit:
ulimit -n 4096 - Lower concurrency for unstable networks:
--concurrency 4-8 - Use
--max-pagesto limit scope on large sites - Run scans from a stable network or via a controlled proxy
Important: Only scan systems you own or have explicit permission to test. Misuse can be illegal.
If you discover a vulnerability:
- Do not exploit it.
- Follow responsible disclosure: contact the site owner/security contact.
- Provide minimal PoC data required to verify.
| Indicator | Meaning / suggested action |
|---|---|
PARA-REFLECT |
Parameter value appears in response — check manually for XSS |
FUZZ-ERR |
Error keywords found after fuzz — possible SQLi or parser error (verify manually) |
FUZZ-LEN |
Large length change on fuzz — inspect response for injection output |
SUSPECT |
Base response contained error keywords — investigate further |
All findings are heuristics. Manual verification is required before any claim.
Contributions welcome. Suggested workflow:
- Fork → create branch → PR
- Follow PEP8 and keep functions small and testable
- Add tests for new analysis logic
- Update
CHANGELOG.mdfor any behavior changes
Planned / optional improvements:
- HTML/interactive report (Streamlit or static HTML)
- Plugin architecture for additional analyzers
- Rate-limiter + politeness settings (random delays)
- Web dashboard + API export (webhook/Discord/Telegram)
- v1.0 — Initial release (core crawling + param mapping)
- v1.1 — Added async parameter analysis: fuzzing, reflection, error keyword detection
MIT License © 2025 Bangladesh Cyber Squad